Third-Party Risk Management (TPRM) is the process of identifying, assessing, monitoring, and mitigating risks associated with external vendors, suppliers, service providers, and business partners. Modern organizations depend heavily on third parties for cloud hosting, SaaS platforms, IT support, payment processing, cybersecurity services, and operational outsourcing.
For banks, fintech companies, healthcare organizations, and enterprises handling sensitive data, weak vendor controls can lead to data breaches, regulatory penalties, operational disruptions, financial fraud, supply chain attacks, and compliance failures. That is why Third-Party Risk Management has become a core component of ISO 27001, SOC 2, RBI outsourcing guidelines, NIST Cybersecurity Framework, PCI DSS, and enterprise GRC programs.
This guide explains everything organizations need to know about TPRM, including frameworks, lifecycle stages, vendor assessments, questionnaires, risk scoring, compliance requirements, automation, and best practices.
1. What is Third-Party Risk Management (TPRM)?
Third-Party Risk Management (TPRM) is a structured process used by organizations to evaluate and continuously monitor risks introduced by vendors, suppliers, contractors, cloud providers, and external service providers.
TPRM ensures third parties maintain adequate security controls, protect sensitive information, meet compliance obligations, operate reliably, and do not expose the organization to unacceptable risk.
TPRM programs typically evaluate cybersecurity controls, data privacy practices, compliance posture, financial stability, operational resilience, business continuity capabilities, access management, and incident response readiness.
2. TPRM Full Form & Meaning
TPRM Full Form: Third-Party Risk Management
TPRM Meaning: A governance and risk management process designed to assess and manage risks associated with external vendors and business partners.
Organizations use TPRM to ensure vendors meet internal security standards, contractual obligations, and regulatory requirements.
3. Why Third-Party Risk Management Is Important
Third-party vendors often have access to sensitive customer data, internal systems, financial records, cloud environments, and production infrastructure. A single weak vendor can compromise an entire enterprise.
Real Business Risks
In real enterprise environments, vendor-related failures rarely begin with sophisticated attacks. Most issues originate from weak operational controls, incomplete assessments, poor monitoring, or lack of governance visibility.
During banking and fintech TPRM assessments, common observations include:
- Shared privileged accounts used by vendor administrators
- Incomplete quarterly access reviews
- Missing DR drill evidence
- Weak SLA monitoring for critical vendors
- Vendors without formal incident response commitments
- Lack of centralized vendor inventory management
- Excessive production access in cloud-hosted environments
Industry Statistics & Research Insights
- According to IBM’s Cost of a Data Breach Report, third-party compromise remains one of the most expensive breach vectors due to delayed containment timelines.
- The Verizon Data Breach Investigations Report (DBIR) has consistently highlighted credential compromise, vendor exposure, and phishing-related supply chain incidents as major contributors to enterprise breaches.
- Industry research from ENISA and CrowdStrike indicates that supply-chain attacks and SaaS-related security incidents have increased significantly.
- Gartner and Ponemon research emphasize that organizations with mature vendor governance generally achieve stronger audit readiness and improved visibility into external dependencies.
Regulatory Expectations
Banks and regulated organizations are expected to assess vendor risk continuously. Frameworks and regulators requiring TPRM include RBI outsourcing guidelines, ISO 27001 Annex A, SOC 2 Trust Criteria, NIST, HIPAA, and PCI DSS.
4. Types of Third-Party Risks
Cybersecurity Risk
Risk arising from weak vendor security controls. Examples: weak MFA implementation, unpatched systems, poor logging and monitoring, weak access controls.
Compliance Risk
Risk that vendors fail to meet legal or regulatory obligations. Examples: GDPR violations, PCI DSS non-compliance, missing audit evidence.
Operational Risk
Risk of service disruption due to vendor failures. Examples: cloud outages, backup failures, incident response gaps.
Financial Risk
Risk related to vendor financial instability. Examples: bankruptcy, cash flow issues, business closure.
Reputational Risk
Negative impact on brand reputation due to vendor incidents. Examples: public data breaches, fraud incidents, customer complaints.
Strategic Risk
Risk arising from poor vendor alignment with business objectives.
5. TPRM Lifecycle (End-to-End)
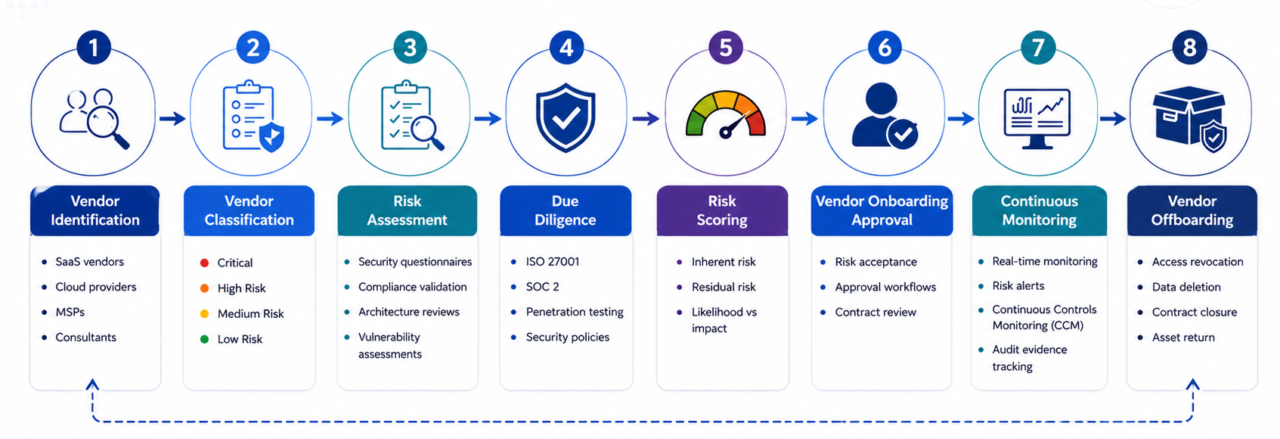
A mature Third-Party Risk Management program follows a structured lifecycle.
1. Vendor Identification
Identify all third parties interacting with organizational systems, data, or operations. Examples: SaaS vendors, cloud providers, managed service providers, payment processors, consultants.
2. Vendor Classification
Categorize vendors based on data sensitivity, system access, business criticality, and regulatory impact. Typical classifications: Critical, High Risk, Medium Risk, Low Risk.
3. Risk Assessment
Conduct vendor security and compliance assessments including security questionnaires, document reviews, compliance validation, architecture reviews, and vulnerability assessments.
4. Due Diligence
Validate vendor claims using evidence. Examples: ISO 27001 certificates, SOC 2 reports, penetration testing reports, security policies, audit reports.
5. Risk Scoring
Assign risk ratings based on identified gaps. Typical ratings: Critical, High, Medium, Low.
6. Vendor Onboarding Approval
Approve or reject vendors based on risk tolerance.
7. Continuous Monitoring
Monitor vendors continuously for security incidents, compliance changes, vulnerability exposure, and risk score changes.
8. Offboarding
Ensure secure termination of vendor access including access revocation, data deletion, contract closure, and asset return.
6. Vendor Risk Assessment Process
In mature organizations, vendor assessments are not treated as one-time procurement activities. They are integrated into enterprise risk management, cybersecurity governance, compliance monitoring, and audit readiness processes.
Effective assessments combine security validation, compliance verification, operational resilience review, evidence-based testing, ongoing oversight, and real-time visibility.
Organizations relying only on vendor questionnaires without evidence validation often develop false confidence in vendor security posture.
Typical Vendor Assessment Areas
- Security Controls: MFA, IAM, encryption, SIEM monitoring, endpoint protection
- Compliance Controls: ISO 27001, SOC 2, GDPR, RBI compliance
- Operational Controls: Backup management, incident response, DR testing, SLA management
- Access Management: Privileged access controls, role-based access, user reviews
- Cloud Security: AWS security posture, Azure controls, logging configuration, cloud monitoring
7. Vendor Risk Assessment Questionnaire
As vendor ecosystems expand, organizations increasingly rely on structured security questionnaires to standardize assessment processes and improve consistency across assessments.
Access Management
- Is MFA enabled?
- Are privileged accounts monitored?
- Are access reviews conducted periodically?
Change Management
- Are changes approved before deployment?
- Is production access restricted?
- Is rollback testing performed?
Incident Response
- Is there an incident response plan?
- Are incidents tracked and investigated?
- Is customer notification process documented?
Data Protection
- Is encryption enabled at rest and in transit?
- Are backups tested regularly?
- Is sensitive data segregated?
Compliance
- Do you maintain ISO 27001 certification?
- Is SOC 2 audit completed?
- Are VAPT assessments conducted annually?
8. Third-Party Risk Assessment Checklist
Governance
- Vendor inventory maintained
- Vendor classification defined
- TPRM policy approved
Security
- MFA enabled
- Logging monitored
- Vulnerability scans conducted
- Endpoint protection active
Compliance
- ISO 27001 evidence available
- SOC 2 reports reviewed
- RBI requirements mapped
Operations
- Backup testing completed
- Incident management process defined
- DR testing performed
Access Management
- Privileged access restricted
- User reviews conducted
- Dormant accounts removed
9. Risk Scoring Methodology
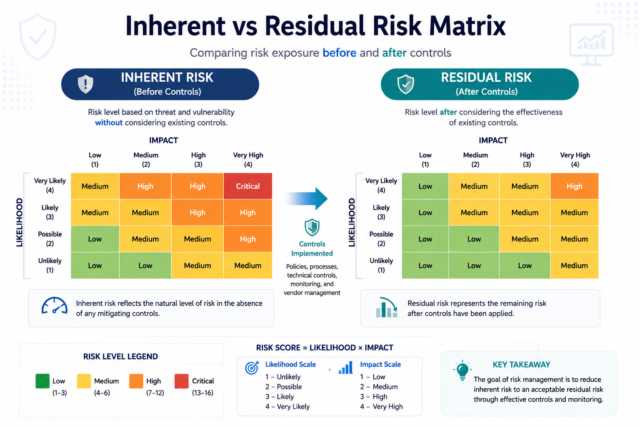
Mature TPRM programs separate inherent vendor risk from residual risk after compensating controls are validated.
Inherent Risk
Inherent risk refers to the level of risk a vendor introduces before security controls or mitigations are evaluated. Common factors include data sensitivity, privileged or production access, regulatory exposure, cloud hosting involvement, critical business dependency, and geographic operations.
Residual Risk
Residual risk represents the remaining exposure after evaluating implemented controls such as MFA enforcement, encryption, SOC 2 reports, SIEM monitoring, DR testing, and incident response maturity.
| Risk Area | Example Criteria |
|---|---|
| Business Criticality | Critical application dependency |
| Data Sensitivity | PII, banking, healthcare, financial data |
| Access Exposure | Administrative or production access |
| Compliance Impact | RBI, ISO 27001, SOC 2 relevance |
| Operational Dependency | Vendor outage business impact |
| Security Maturity | Logging, monitoring, MFA, IR readiness |
10. TPRM Framework Components
- Governance Structure – Defines ownership, policies, and approval workflows
- Risk Methodology – Defines how vendor risk is assessed and scored
- Assessment Workflows – Standardized onboarding and review processes
- Continuous Monitoring – Persistent monitoring for critical vendors, outsourced environments, and cloud service providers
- Reporting & Dashboards – Executive-level visibility into vendor risk posture
- Remediation Tracking – Tracks vendor findings and corrective actions
11. TPRM Roles & Responsibilities
| Team | Responsibility |
|---|---|
| Security Team | Vendor security validation and control assessment |
| Compliance Team | Regulatory mapping and compliance oversight |
| Procurement Team | Vendor onboarding and coordination |
| Legal Team | Contractual obligations and DPA review |
| Internal Audit | Independent review and assurance validation |
| IT Operations | Integration and operational monitoring |
| Business Owners | Vendor relationship and SLA oversight |
12. Fourth-Party Risk Management
Fourth-party risk refers to risks introduced by a vendor’s own suppliers, subcontractors, cloud providers, or downstream service dependencies.
- SaaS vendors relying on cloud infrastructure providers
- Managed service providers outsourcing support operations
- Payment gateways depending on external hosting vendors
- Software vendors integrating third-party APIs
Mature organizations increasingly require vendors to disclose critical subcontractors, cloud dependencies, and inherited controls as part of due diligence and continuous monitoring activities.

13. Third-Party Risk Management for Banks
Banks and financial institutions face elevated regulatory expectations. The Reserve Bank of India (RBI) has significantly increased focus on outsourcing governance, cybersecurity controls, auditability, cloud outsourcing oversight, and ongoing vendor assurance for regulated entities.
RBI Expectations
- Vendor due diligence before onboarding
- Continuous monitoring of outsourced services
- Preservation of audit evidence and logs
- Incident reporting obligations
- Business continuity and disaster recovery validation
- Governance over cloud-hosted environments
- Periodic reassessment of critical vendors
Common Banking Vendor Risks
- Core banking outsourcing
- Cloud hosting providers
- Payment gateway integrations
- Fintech API exposure
- Shared infrastructure risks
14. Common Vendor Risk Assessment Findings
- Shared admin accounts
- Weak MFA implementation
- Missing access reviews
- No DR testing evidence
- Incomplete logging
- Weak vendor onboarding
- Missing contractual security clauses
- Lack of continuous monitoring
15. Automated Vendor Risk Management
Traditional TPRM programs often rely heavily on spreadsheets, emails, manual questionnaires, disconnected evidence repositories, and fragmented workflows—creating operational challenges including delayed assessments, inconsistent risk scoring, missing audit evidence, and audit preparation delays.
Organizations replacing spreadsheet-based TPRM processes typically experience faster vendor onboarding, improved audit readiness, better risk visibility, reduced manual effort, centralized evidence management, continuous vendor monitoring, and improved remediation tracking.
Benefits of Automation
- Faster assessments
- Reduced audit effort
- Real-time monitoring
- Automated evidence collection
- Centralized vendor tracking
- Improved reporting
Common TPRM Automation Features
- Vendor onboarding workflows
- Risk scoring engines
- Questionnaire automation
- Compliance mapping
- Dashboard reporting
- SLA tracking
- Continuous monitoring
16. Continuous Third-Party Monitoring
Traditional TPRM relied on annual assessments. Modern organizations now implement Continuous Controls Monitoring (CCM), API-based evidence collection, security rating integrations, and real-time risk alerts.
Ongoing oversight improves visibility into vendor security posture, compliance readiness, incident response coordination, and early detection of operational risk.
17. TPRM vs VRM vs Supplier Risk Management
| Aspect | TPRM | VRM | Supplier Risk Management |
|---|---|---|---|
| Primary Focus | Enterprise third-party risk | Vendor-specific governance | Supply chain continuity |
| Key Risks | Cybersecurity, compliance, operational | Vendor performance and risk oversight | Manufacturing and logistics disruption |
| Typical Teams | Security, GRC, Audit | Procurement, Risk, Compliance | Supply chain and operations |
18. TPRM Maturity Model
| Level | Maturity | Description |
|---|---|---|
| Level 1 | Reactive | Manual vendor reviews |
| Level 2 | Defined | Policies documented |
| Level 3 | Managed | Periodic assessments |
| Level 4 | Automated | Workflow automation |
| Level 5 | Optimized | Continuous risk monitoring |
Organizations moving from Level 2 to Level 4 typically experience reduced audit effort, faster vendor onboarding, better compliance readiness, and improved risk visibility.
Ready to advance your TPRM maturity?
Learn how ASPIA helps banks and enterprises automate vendor assessments, evidence collection, and continuous monitoring.
Request an ASPIA Demo19. Best Practices for Third-Party Risk Management
- Maintain a Central Vendor Inventory – Track all vendors and associated risks
- Classify Vendors Properly – Not all vendors carry the same level of risk
- Automate Assessments – Reduce manual effort using workflow automation
- Perform Continuous Monitoring – Avoid relying only on annual reviews
- Integrate TPRM With GRC Programs – Align vendor risk with enterprise risk management
- Validate Evidence – Never rely solely on vendor statements
20. Frequently Asked Questions (FAQs)
What is TPRM?
Why is TPRM important?
What is a vendor risk assessment?
What frameworks support TPRM?
What is continuous vendor monitoring?
21. Final Thoughts
Third-Party Risk Management is no longer optional. As organizations increasingly rely on cloud providers, SaaS vendors, outsourced services, and interconnected supply chains, vendor risk becomes enterprise risk.
Organizations that implement mature TPRM programs achieve better regulatory readiness, stronger cybersecurity posture, faster vendor onboarding, improved audit outcomes, and reduced operational disruptions.
Modern TPRM is shifting from periodic assessments to continuous risk monitoring powered by automation, integrations, and real-time evidence collection.
Modernize Third-Party Risk Management With Aspia
Aspia helps organizations streamline and automate vendor onboarding, risk assessments, security questionnaires, evidence collection, risk scoring, ongoing security validation, audit reporting, and remediation tracking.
- ✓ Automated vendor assessment workflows
- ✓ Centralized evidence repositories
- ✓ Continuous Controls Monitoring (CCM)
- ✓ Risk dashboards and reporting
- ✓ Integration with AWS, Azure, JIRA, GitHub, SIEM platforms, and identity providers
- ✓ Audit-ready reporting with evidence lineage
- ✓ Workflow automation for remediation tracking
Replace spreadsheet-based vendor assessments with centralized workflow automation.
Request an ASPIA Demo