ITGC is often underestimated until something breaks. Weak IT controls can lead to unauthorized financial transactions, production outages due to untested changes, data breaches from excessive access privileges, and audit failures with regulatory penalties. According to industry breach studies, compromised credentials and weak access management remain among the most common causes of security incidents—which directly ties back to ITGC failures.
An ITGC audit (Information Technology General Controls audit) is a structured evaluation of foundational IT controls—covering access management, change management, IT operations, and security—to ensure that systems are secure, reliable, and compliant with frameworks such as ISO 27001, SOC 2, and RBI guidelines.
This guide provides a complete framework for understanding ITGC audits—from control domains and testing methodology to design vs operating effectiveness, real audit evidence, cloud controls, maturity models, and how automation transforms ITGC from annual compliance events into continuous control monitoring.
1. What Is ITGC Audit? Definition & Purpose
An ITGC audit (Information Technology General Controls audit) is a structured evaluation of foundational IT controls—covering access management, change management, IT operations, and security—to ensure that systems are secure, reliable, and compliant with frameworks such as ISO 27001, SOC 2, and RBI guidelines.
ITGC audits validate whether controls are not only documented but consistently operating under real-world conditions—where most failures actually occur.
ITGC forms the backbone of financial audits (ICFR/SOX), ISO 27001 certification, SOC 2 assurance, RBI compliance, and vendor risk assessments.
2. Why ITGC Audits Are Critical (With Real Risk Context)
Weak IT controls can lead to:
- Unauthorized financial transactions
- Production outages due to untested changes
- Data breaches from excessive access privileges
- Audit failures and regulatory penalties
According to industry breach studies, compromised credentials and weak access management remain among the most common causes of security incidents—which directly ties back to ITGC failures.
That’s why ITGC forms the backbone of financial audits (ICFR/SOX), ISO 27001 certification, SOC 2 assurance, RBI compliance, and vendor risk assessments.
3. Core Domains of ITGC Controls
ITGC controls are structured into four domains, each addressing a distinct risk layer.

Access Management
Controls how users interact with systems. Auditors evaluate whether access is granted based on roles, reviewed periodically, and revoked promptly. Weak access controls are one of the most frequent audit findings.
Change Management
Ensures that system changes are approved, tested, and traceable. In real audits, uncontrolled production changes are a high-risk red flag.
IT Operations
Focuses on system reliability—backups, monitoring, incident handling. Failures here directly impact business continuity.
Security Controls
Protect infrastructure and data through encryption, firewalls, and monitoring. Auditors assess both configuration and effectiveness.
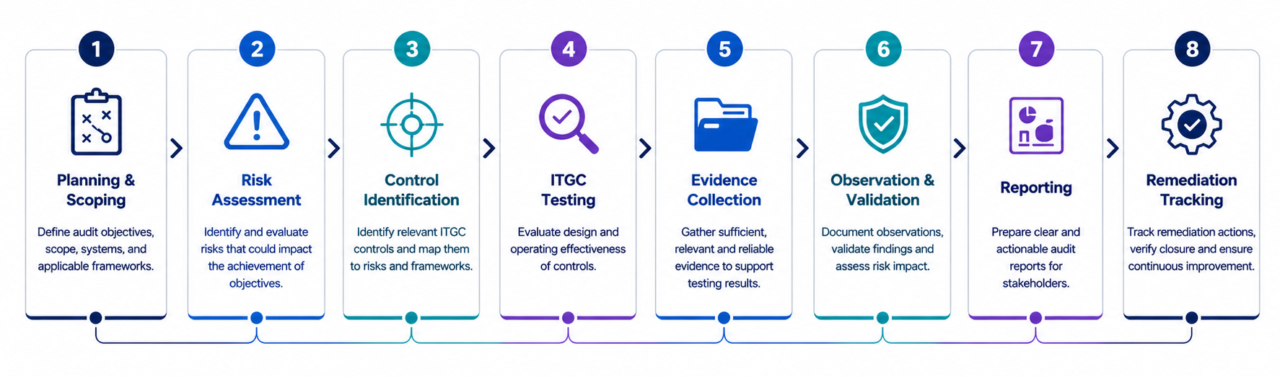
4. How Auditors Perform ITGC Testing (Real Audit Methodology)
ITGC audits follow a structured methodology grounded in evidence—not assumptions.
Walkthroughs
Auditors begin by understanding how a control operates in practice. For example, they may trace a user access request from submission to approval and provisioning.
Sampling
Auditors use sampling techniques to test control execution. Instead of reviewing all records, they select representative samples—such as a set of user accounts or change requests—to evaluate consistency.
Inquiry and Observation
Auditors validate whether teams actually follow documented processes. This is critical because many organizations have “paper controls” that are not operational.
Re-performance and Evidence Validation
Auditors independently verify whether controls worked as intended using logs, tickets, and configurations.
5. ITGC Testing: Design Effectiveness vs Operating Effectiveness
One of the most misunderstood areas in ITGC audits is the difference between Design Effectiveness (DE) and Operating Effectiveness (OE). Auditors evaluate both to determine whether controls are not only defined but also working in practice.
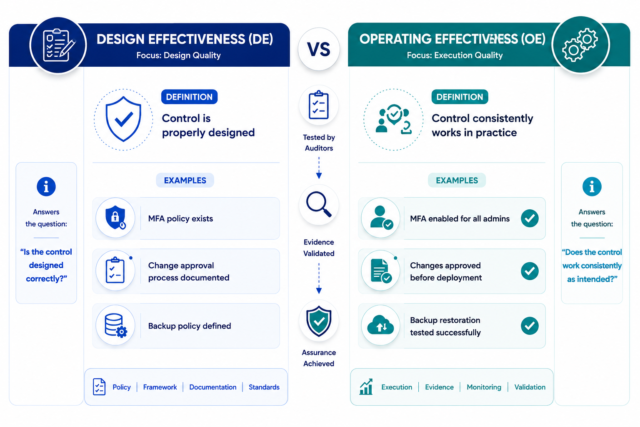
| Type | Meaning | Example |
|---|---|---|
| Design Effectiveness (DE) | Control is properly designed to mitigate risk if executed as intended | MFA policy is defined in the security policy requiring all admin users to enable MFA |
| Operating Effectiveness (OE) | Control consistently works in practice across all relevant instances | MFA is enabled for all admin users (evidence: sampled users have MFA enforced) |
- DE focuses on design → policies, procedures, and control structure
- OE focuses on execution → actual implementation, consistency, and evidence
In real audits, most failures occur not because controls are missing—but because they are not consistently followed.
6. ITGC Control Testing (Practical Deep Dive)
Access Control Testing
Auditors analyze user access listings and compare them with defined roles. They validate whether terminated users are removed promptly and whether privileged access is restricted. Evidence such as IAM configurations and access review reports is examined to ensure enforcement.
Change Management Testing
Instead of simply checking if a process exists, auditors review actual change tickets to confirm that approvals, testing, and deployments follow a controlled workflow. Unauthorized or emergency changes are scrutinized heavily.
IT Operations Testing
Auditors review backup execution logs and restoration testing reports to verify that recovery processes are reliable. They also assess whether incidents are tracked, investigated, and resolved within defined timelines.
Security Control Testing
Security configurations are validated against best practices. Auditors review firewall rules, encryption settings, and monitoring alerts to ensure that threats can be detected and mitigated.
7. ITGC Audit Evidence Examples
| Control Area | Evidence |
|---|---|
| Access | IAM user lists, access review reports |
| Change | JIRA/Bitbucket approvals, change tickets |
| Logging | CloudTrail logs, SIEM alerts |
| Backup | Restore test reports, backup logs |
| MFA | Identity provider screenshots |
| Monitoring | SIEM alert logs, incident tickets |
8. ITGC Control Matrix (Audit-Ready)
| Control Area | Objective | Testing Procedure | Evidence |
|---|---|---|---|
| Access | Prevent unauthorized access | Sample user validation | IAM reports |
| Change | Ensure controlled changes | Ticket review | JIRA logs |
| Backup | Ensure recovery capability | Restore testing | Backup logs |
| Logging | Maintain audit trail | Log validation | CloudTrail |
9. ITGC Maturity Model
Assess your organization’s ITGC capability using this five-level maturity model.

| Level | Maturity | Description |
|---|---|---|
| Level 1 | Reactive | Ad-hoc processes, manual controls |
| Level 2 | Defined | Documented policies exist |
| Level 3 | Managed | Periodic testing and reviews |
| Level 4 | Automated | Automated monitoring and alerts |
| Level 5 | Optimized | Continuous compliance with real-time insights |
Organizations moving from Level 2 → Level 4 typically see: 40–60% reduction in audit effort, faster compliance cycles, and fewer audit observations.
Ready to advance your ITGC maturity?
Learn how ASPIA’s GRC platform helps organizations automate ITGC testing, evidence collection, and continuous control monitoring.
Request an ASPIA Demo10. Sample ITGC Audit Observation (Real-World)
Observation: Developers had direct production access in AWS.
Risk: Uncontrolled changes may impact system stability, data integrity, and security. Direct access bypasses change management controls.
Recommendation: Implement role-based access controls and enforce segregation of duties with approval workflows.
11. ITGC in AWS & Cloud Environments
Modern ITGC audits are cloud-centric.
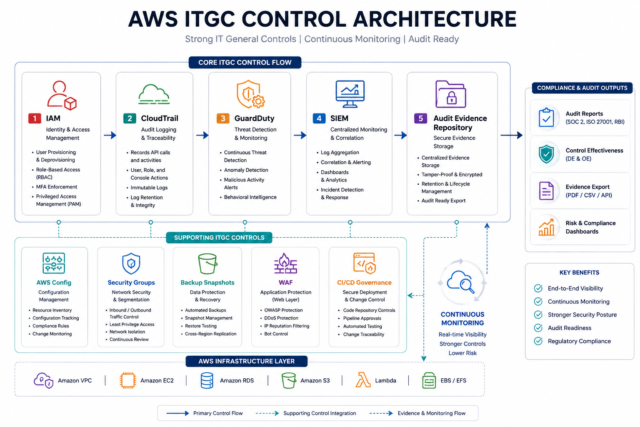
Key controls include:
- IAM – least privilege access with regular reviews
- CloudTrail – audit logging for all API calls
- Security Groups – network-level access controls
- Encryption – data protection at rest and in transit
- Backup snapshots – automated backups with restore testing
Advanced controls: AWS Config (compliance monitoring), GuardDuty (threat detection), WAF (web application firewall), CI/CD governance.
12. Common ITGC Audit Findings
- Shared admin accounts
- Missing access reviews
- Direct production access
- Unapproved changes
- Backup not tested
- Logs not monitored
13. Common Mistakes Organizations Make
- Treating ITGC as documentation-only exercise
- Manual evidence tracking (high audit friction)
- No periodic access certification
- Weak log retention policies
- Lack of segregation of duties
14. Automated ITGC Testing & Continuous Monitoring
The shift is clear: From annual audits → Continuous Controls Monitoring (CCM).
- API-based evidence collection
- DevOps integrations (JIRA, GitHub, Jenkins)
- Real-time alerting for control failures
- Automated evidence repositories
This significantly reduces audit fatigue.
15. Frequently Asked Questions (FAQs)
What is ITGC audit?
What are ITGC controls?
What is ITGC testing?
What is a walkthrough in ITGC audit?
What is automated ITGC testing?
What is segregation of duties in ITGC?
16. Final Takeaway
ITGC audits are not just compliance exercises—they are the foundation of secure, reliable, and auditable IT operations. Organizations that move from manual, annual ITGC testing to automated, continuous control monitoring reduce audit effort by 40–60%, achieve faster compliance cycles, and significantly reduce audit observations.
If your ITGC evidence is still collected manually, your audit is already at risk—regardless of control design.
Automate ITGC Testing with ASPIA
ASPIA’s GRC platform automates ITGC evidence collection, control testing, and continuous monitoring—reducing audit effort and ensuring audit readiness.
- ✓ Automated evidence collection from IAM, JIRA, CloudTrail, and other sources
- ✓ Continuous control monitoring with real-time alerts
- ✓ Design effectiveness and operating effectiveness testing workflows
- ✓ Integration with AWS, Azure, JIRA, GitHub, and identity providers
- ✓ Audit-ready reports with complete evidence lineage
- ✓ 40–60% reduction in audit preparation effort
If your ITGC evidence is still collected manually, your audit is already at risk. Aspia ensures it isn’t.
Request an ASPIA Demo