The RBI Cyber Security Framework (CSF) is one of the most important cybersecurity and regulatory compliance requirements for banks, NBFCs, financial institutions, and regulated entities operating in India. The Reserve Bank of India (RBI) introduced cybersecurity and cyber resilience expectations to strengthen banking security posture, cyber resilience, IT governance, operational risk management, incident response readiness, third-party risk management, and auditability and compliance monitoring.
As banks increasingly adopt cloud infrastructure, digital banking platforms, mobile applications, fintech integrations, outsourced vendors, and SaaS ecosystems, cybersecurity risk exposure has increased significantly. The RBI Cyber Security Framework helps organizations establish structured controls, governance processes, monitoring capabilities, and audit mechanisms to reduce cyber risk and improve operational resilience.
This guide explains the RBI Cyber Security Framework for banks, including RBI cybersecurity guidelines, cyber security controls, compliance requirements, audit expectations, implementation challenges, evidence collection, cloud governance, third-party risk management, continuous monitoring, and best practices.
1. Key RBI Cyber Security Circulars & Regulatory References
The RBI Cyber Security Framework is supported by multiple regulatory expectations, circulars, and operational governance directives issued for banks, NBFCs, payment systems, and regulated financial entities.
| RBI Cyber Security Framework Quick Facts | |
|---|---|
| Issued By | Reserve Bank of India (RBI) |
| Primary Circular | Cyber Security Framework in Banks (2016) |
| Applies To | Banks, NBFCs, regulated financial entities |
| Focus Areas | Cyber resilience, governance, monitoring, incident response |
| Key Requirement | Continuous monitoring & auditability |
| Major Control Areas | IAM, SIEM, VAPT, TPRM, Incident Response |
| Audit Focus | Evidence validation & operational effectiveness |
| Modern Focus | Continuous Controls Monitoring (CCM) |
Common RBI Regulatory Areas
- RBI Cyber Security Framework guidance for banks — RBI Cyber Security Framework in Banks (2016)
- RBI outsourcing and third-party risk management expectations — RBI Master Direction on Managing Risks and Code of Conduct in Outsourcing of Financial Services
- RBI digital payment security controls — RBI Directions on Digital Payment Security Controls
-
RBI NBFC cybersecurity expectations — RBI Master Direction – Information Technology Framework for the NBFC Sector
- RBI Master Direction on IT Governance, Risk, Controls and Assurance Practices – RBI Master Direction on IT Governance, Risk, Controls and Assurance Practices (2023)
- RBI Guidelines on Digital Lending – RBI Guidelines on Digital Lending (2022)
Official RBI References & Regulatory Guidance
Key RBI references include: RBI Cyber Security Framework in Banks (2016), RBI Master Direction on Outsourcing of Financial Services, RBI IT Framework for NBFCs, RBI Cyber Crisis Management Plan (CCMP), RBI Digital Payment Security Controls, and RBI IT Governance and Assurance Expectations.
2. What is the RBI Cyber Security Framework?
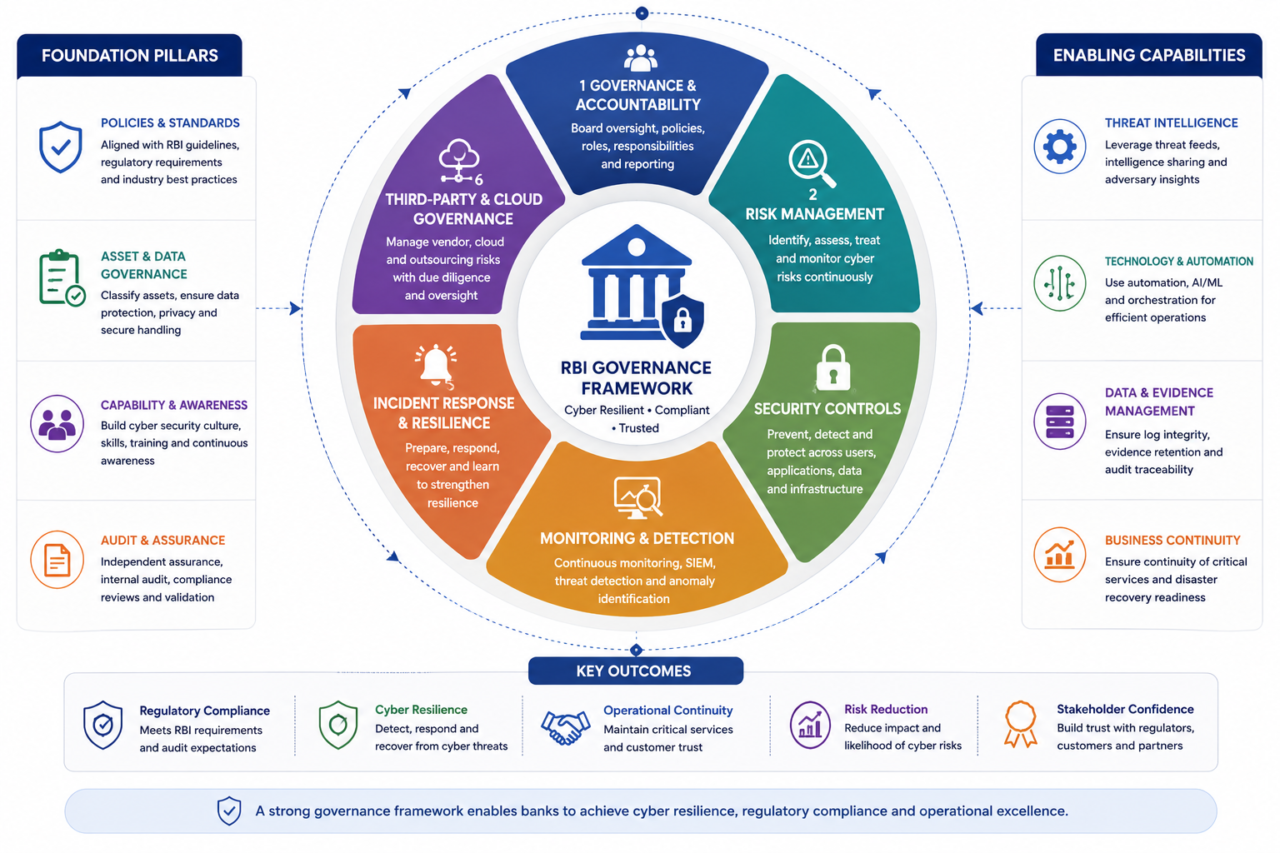
The RBI Cyber Security Framework is a set of cybersecurity governance, monitoring, operational resilience, and compliance expectations issued by the Reserve Bank of India for regulated financial entities.
The framework focuses on cyber resilience, security governance, operational monitoring, incident management, auditability, vendor risk management, data protection, infrastructure security, and continuous security monitoring.
The objective is to ensure banks maintain strong cybersecurity controls, proactive threat monitoring, timely incident response, secure digital operations, effective governance mechanisms, and operational continuity.
3. Why the RBI Cyber Security Framework Is Important
Cyberattacks targeting banks and financial institutions continue to increase globally. Financial institutions frequently face ransomware attacks, phishing campaigns, credential compromise, insider threats, API attacks, cloud security exposure, supply-chain attacks, and vendor compromise.
Weak cybersecurity governance can result in regulatory penalties, operational disruption, financial loss, reputational damage, data breaches, and customer trust erosion.
Industry Statistics & Research Insights
- According to IBM’s Cost of a Data Breach Report, financial services organizations remain among the most heavily targeted sectors globally.
- The Verizon DBIR consistently highlights credential compromise, phishing, and third-party exposure as major contributors to banking-sector breaches.
- Research from Gartner, ENISA, and CrowdStrike indicates that cloud-related attacks are increasing, third-party cyber risk continues to grow, and ransomware attacks are becoming more sophisticated.
4. RBI Cyber Security Framework Objectives
- Strengthen cybersecurity posture
- Improve cyber resilience
- Establish governance accountability
- Implement risk-based controls
- Improve monitoring capabilities
- Detect threats proactively
- Reduce operational risk
- Maintain compliance readiness
5. Key Components of the RBI Cyber Security Framework
1. Cyber Security Governance
Banks are expected to establish strong cybersecurity governance structures including board-level cybersecurity oversight, defined security policies, risk management frameworks, security governance committees, cybersecurity accountability models, and regulatory reporting mechanisms.
Common Audit Observations: weak governance ownership, missing security metrics, lack of board reporting, inconsistent policy reviews, inadequate risk escalation.
2. IT & Information Security Controls
Banks must implement strong security controls including MFA, IAM, privileged access controls, encryption controls, network segmentation, endpoint protection, vulnerability management, patch management, and security monitoring.
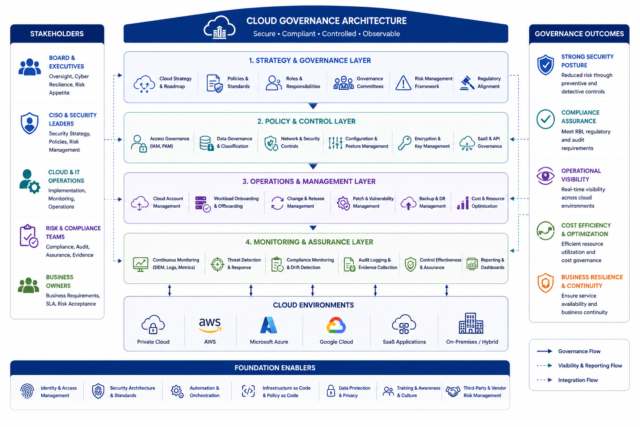
Cloud Security Governance: As banks increasingly adopt cloud services, RBI expectations around cloud governance continue to expand including shared responsibility models, cloud access governance, multi-tenant SaaS exposure, CSP dependency management, cloud logging and monitoring, and workload segregation.
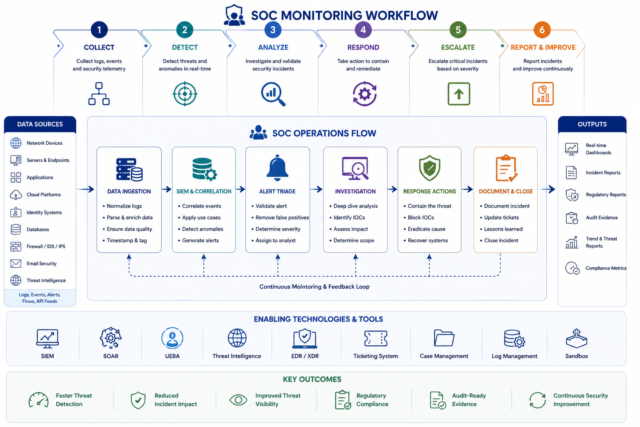
3. Security Operations Center (SOC) Monitoring
RBI strongly emphasizes continuous security monitoring including SIEM monitoring, log collection, threat detection, alert management, incident escalation, continuous monitoring, and threat intelligence integration.
Common Evidence Reviewed: SIEM alerts, security dashboards, incident tickets, threat investigation records, monitoring reports, log retention evidence.
4. Incident Response & Cyber Resilience
Banks must maintain mature incident response and cyber resilience capabilities including incident response plans, escalation procedures, root cause analysis, regulatory reporting, cyber drill exercises, recovery validation, and business continuity testing.
Common Audit Findings: Missing incident evidence, weak escalation workflows, incomplete RCA documentation, delayed incident reporting, lack of cyber drill evidence.
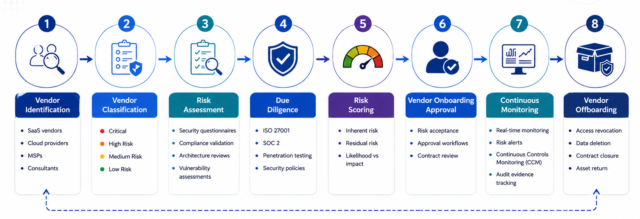
5. Third-Party Risk Management (TPRM)
RBI places significant emphasis on vendor governance including vendor due diligence, security assessments, vendor monitoring, contractual security clauses, cloud outsourcing governance, subcontractor visibility, and periodic reassessment.
Common Vendor Risks: Weak vendor security posture, lack of audit evidence, poor cloud governance visibility, shared infrastructure exposure, weak subcontractor oversight.
6. Vulnerability Management & Patch Management
Banks are expected to maintain strong vulnerability management programs including regular vulnerability assessments, penetration testing, patch deployment tracking, remediation workflows, risk prioritization, and asset visibility.
Common Operational Challenges: incomplete asset inventories, delayed remediation, inconsistent patching, fragmented vulnerability reporting, spreadsheet-based tracking.
7. Audit Logging & Evidence Collection
RBI expectations increasingly emphasize auditability, evidence traceability, and operational visibility. Common audit evidence includes access review reports, SIEM monitoring evidence, incident response records, DR drill reports, vulnerability remediation evidence, MFA enforcement screenshots, CloudTrail logs, and vendor assessment reports.
Mature organizations increasingly move toward evidence-based assurance models supported by automated evidence collection and Continuous Controls Monitoring (CCM).
6. RBI Cyber Security Framework Compliance Checklist
Governance Controls
- Cybersecurity policy approved
- Governance committees established
- Board oversight implemented
- Risk reporting mechanisms defined
Security Controls
- MFA enabled
- IAM controls implemented
- Encryption enforced
- Vulnerability management active
- Endpoint security enabled
Monitoring Controls
- SIEM monitoring active
- Log retention configured
- Alert escalation workflows defined
- Threat monitoring implemented
Incident Response Controls
- IR plan documented
- Escalation matrix defined
- Cyber drills conducted
- RCA documentation maintained
Vendor Governance Controls
- Vendor due diligence completed
- Third-party assessments performed
- Cloud outsourcing reviewed
- Vendor monitoring implemented
Audit & Compliance Controls
- Audit evidence centralized
- Evidence traceability maintained
- Compliance reports reviewed
- Audit workflows documented
7. RBI Cyber Security Framework Audit Process
1. Scope Definition
Identify critical systems, cloud environments, digital banking systems, vendor dependencies, and regulatory obligations.
2. Control Review
Evaluate governance and security controls.
3. Evidence Validation
Validate audit logs, approvals, monitoring evidence, security configurations, and remediation evidence.
4. Vulnerability & Security Assessment
Review VAPT reports, remediation timelines, patching workflows, and threat monitoring evidence.
5. Reporting & Remediation
Document findings, observations, risk ratings, and remediation recommendations.
8. Common RBI Cyber Security Audit Findings
- Weak MFA implementation
- Inconsistent log retention
- Missing backup restoration evidence
- Delayed vulnerability remediation
- Poor vendor governance visibility
- Lack of continuous monitoring
- Incomplete cloud governance reviews
- Fragmented audit evidence
- Spreadsheet-based compliance tracking
- Weak incident response documentation
9. Common Cybersecurity Governance Metrics
| Metric | Purpose |
|---|---|
| MTTR (Mean Time to Respond) | Measures incident response efficiency |
| Incident Escalation Timelines | Tracks response and escalation maturity |
| Patch SLA Adherence | Measures remediation compliance |
| MFA Coverage Percentage | Validates access control maturity |
| Control Compliance Percentage | Tracks governance effectiveness |
| Vendor Reassessment Completion Rate | Measures third-party governance maturity |
| Vulnerability Remediation Timelines | Tracks operational risk reduction |
| Audit Finding Closure Rate | Measures remediation effectiveness |
10. Continuous Controls Monitoring (CCM) & Continuous Assurance
Modern banking environments increasingly require continuous governance visibility. Organizations are moving from periodic assessments toward Continuous Controls Monitoring (CCM), continuous evidence validation, control health monitoring, real-time compliance drift detection, automated governance workflows, and persistent monitoring.
Benefits of CCM
- Faster issue detection
- Improved audit readiness
- Better operational visibility
- Reduced manual effort
- Stronger compliance governance
- Improved cyber resilience
11. Manual vs Automated RBI Compliance Management
| Manual Compliance Processes | Automated Compliance Management |
|---|---|
| Spreadsheet-based tracking | Centralized governance platforms |
| Manual evidence collection | Automated evidence workflows |
| Fragmented audit records | Evidence lineage and traceability |
| Delayed reporting | Real-time compliance visibility |
| Manual remediation tracking | Workflow automation |
| Periodic reviews | Continuous monitoring |
| Higher operational overhead | Centralized governance visibility |
12. Challenges in RBI Cyber Security Framework Implementation
- Fragmented tooling
- Inconsistent governance processes
- Manual audit preparation
- Evidence collection gaps
- Limited cloud visibility
- Vendor assessment fatigue
- Weak cross-functional coordination
- Lack of centralized dashboards
- Delayed remediation tracking
- Inconsistent control monitoring
13. RBI Cyber Security Framework Best Practices
- Establish Board-Level Governance – Ensure executive and board visibility into cybersecurity risks
- Implement Continuous Monitoring – Move beyond annual compliance reviews
- Centralize Audit Evidence – Maintain structured evidence repositories
- Strengthen Vendor Governance – Continuously monitor third-party risk exposure
- Improve Cloud Governance – Validate cloud controls, logging, and workload segregation
- Automate Compliance Workflows – Reduce spreadsheet dependency and improve audit readiness
- Implement Continuous Assurance – Adopt evidence-based governance and automated control validation
14. How Aspia Helps With RBI Cyber Security Framework Compliance
Aspia helps banks and enterprises automate compliance workflows, audit evidence collection, vendor governance, vulnerability management, remediation tracking, audit reporting, continuous monitoring, risk management, and governance visibility.
Key Capabilities
- Continuous Controls Monitoring (CCM)
- Centralized evidence repositories
- Workflow automation
- Risk dashboards
- Vendor risk management
- Audit traceability
- Evidence lineage tracking
- Remediation management
- Compliance reporting
- Integration with cloud and security platforms
Organizations implementing automated governance workflows commonly achieve faster audits, reduced operational effort, better compliance visibility, stronger audit readiness, improved governance maturity, reduced evidence gaps, and faster remediation tracking.
Ready to automate RBI cyber security compliance?
Learn how ASPIA helps banks automate compliance workflows, evidence collection, and continuous monitoring.
Request an ASPIA Demo15. Frequently Asked Questions (FAQs)
What is the RBI Cyber Security Framework?
Who must comply with RBI cybersecurity guidelines?
What are common RBI cyber security controls?
What is Continuous Controls Monitoring (CCM)?
What are common RBI audit findings?
16. Final Thoughts
As banks increasingly operate across interconnected cloud ecosystems, digital banking platforms, fintech integrations, and outsourced environments, cybersecurity governance has evolved from a technical function into a core operational resilience requirement.
The RBI Cyber Security Framework helps organizations establish structured governance, cyber resilience, operational visibility, audit readiness, evidence-based assurance, vendor oversight, and continuous compliance monitoring.
Organizations implementing mature cybersecurity governance programs achieve stronger resilience, faster audits, improved compliance readiness, reduced operational risk, better visibility into security posture, and stronger regulator confidence.
Modernize RBI Cyber Security Compliance With Aspia
Aspia helps organizations automate RBI compliance workflows, cybersecurity governance, evidence collection, Continuous Controls Monitoring (CCM), vendor governance, remediation tracking, audit reporting, risk management, and compliance visibility.
- ✓ Automated compliance workflows
- ✓ Centralized evidence repositories
- ✓ Continuous Controls Monitoring (CCM)
- ✓ Vendor risk management
- ✓ Audit-ready reporting dashboards
- ✓ Integration with cloud and security platforms
- ✓ Evidence lineage and traceability
Reduce spreadsheet-driven compliance tracking with centralized governance automation.
Request an ASPIA Demo